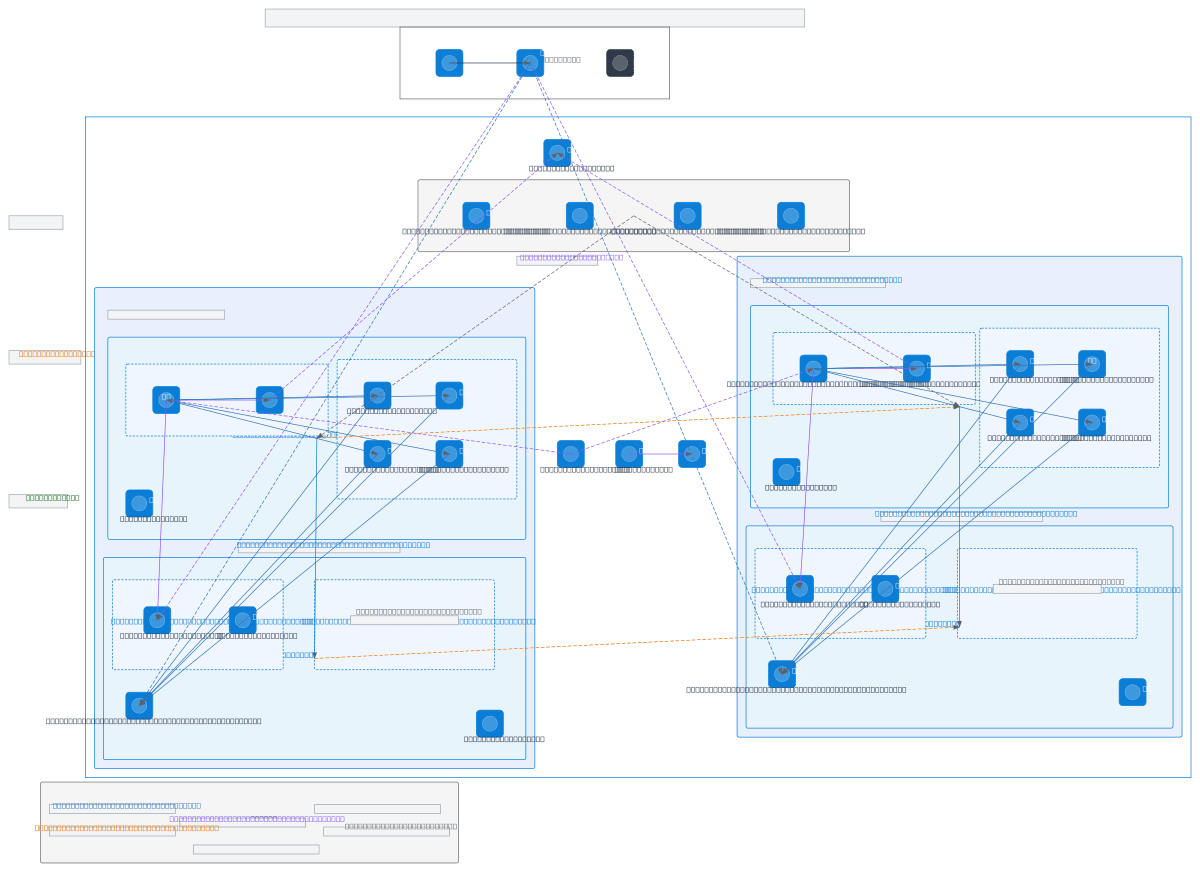
Azure Multi-Region Private Endpoint Architecture
About This Architecture
Multi-region Azure enterprise architecture spanning Australia East and Australia Southeast with isolated application and shared services VNets in each region. Private endpoints for Blob, Queue, Table, File Storage, and Key Vault eliminate public internet exposure while VNet peering enables intra-region connectivity and cross-region replication. Function App Premium instances with system-assigned managed identities and RBAC enforce least-privilege access, with Azure AD Entra ID and service principal authentication securing external integrations. This design demonstrates zero-trust networking principles, reducing attack surface while maintaining high availability across geographically distributed regions. Fork and customize this diagram on Diagrams.so to adapt subnet ranges, add additional regions, or integrate your own Azure services.
People also ask
How do I design a multi-region Azure architecture that eliminates public endpoints and enforces zero-trust security with private endpoints and managed identities?
This diagram shows a production-grade multi-region Azure design with private endpoints for Storage and Key Vault, VNet peering for intra-region connectivity, and system-assigned managed identities with RBAC for least-privilege access. Function App Premium instances integrate with delegated subnets, while NSGs and Private DNS Zones ensure traffic isolation and secure name resolution across Australi
- Domain:
- Cloud Azure
- Audience:
- Azure solutions architects designing multi-region enterprise networks with private endpoints
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.