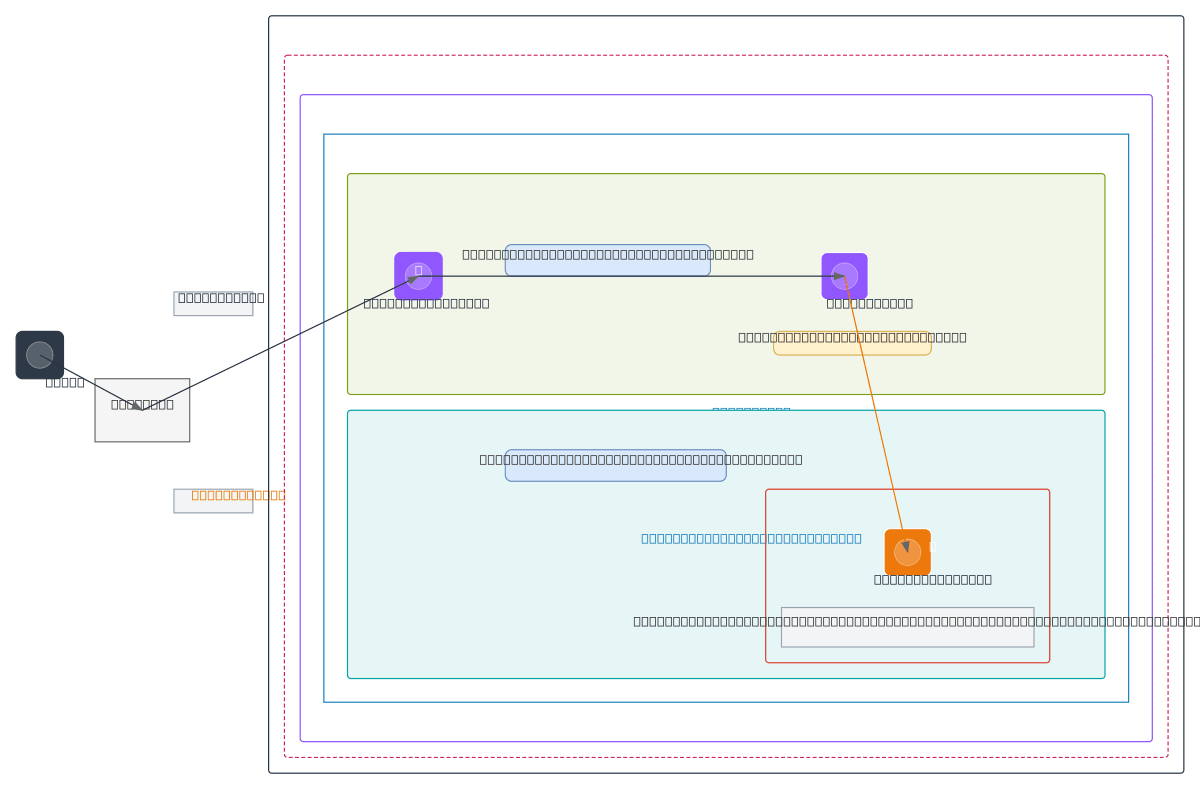
AWS VPC - Public and Private Subnet Architecture
About This Architecture
AWS VPC with public and private subnets across us-east-1a demonstrates a foundational network isolation pattern using Internet Gateway and NAT Gateway. Internet traffic routes through the public subnet's IGW, while private subnet EC2 instances access external resources via NAT Gateway, maintaining inbound security. This architecture enforces least-privilege access with separate security groups controlling SSH from bastion hosts and HTTPS within the VPC. Fork this diagram to customize CIDR blocks, add multi-AZ redundancy, or extend with additional private subnets for databases and caches.
People also ask
How do I design an AWS VPC with public and private subnets using Internet Gateway and NAT Gateway?
This diagram shows a secure VPC (10.0.0.0/16) split into public subnet (10.0.1.0/24) with Internet Gateway for inbound traffic and private subnet (10.0.2.0/24) with NAT Gateway for outbound-only access. Security groups restrict EC2 inbound to SSH from bastion and HTTPS from within the VPC, implementing least-privilege network access.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure, scalable VPC networks
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.