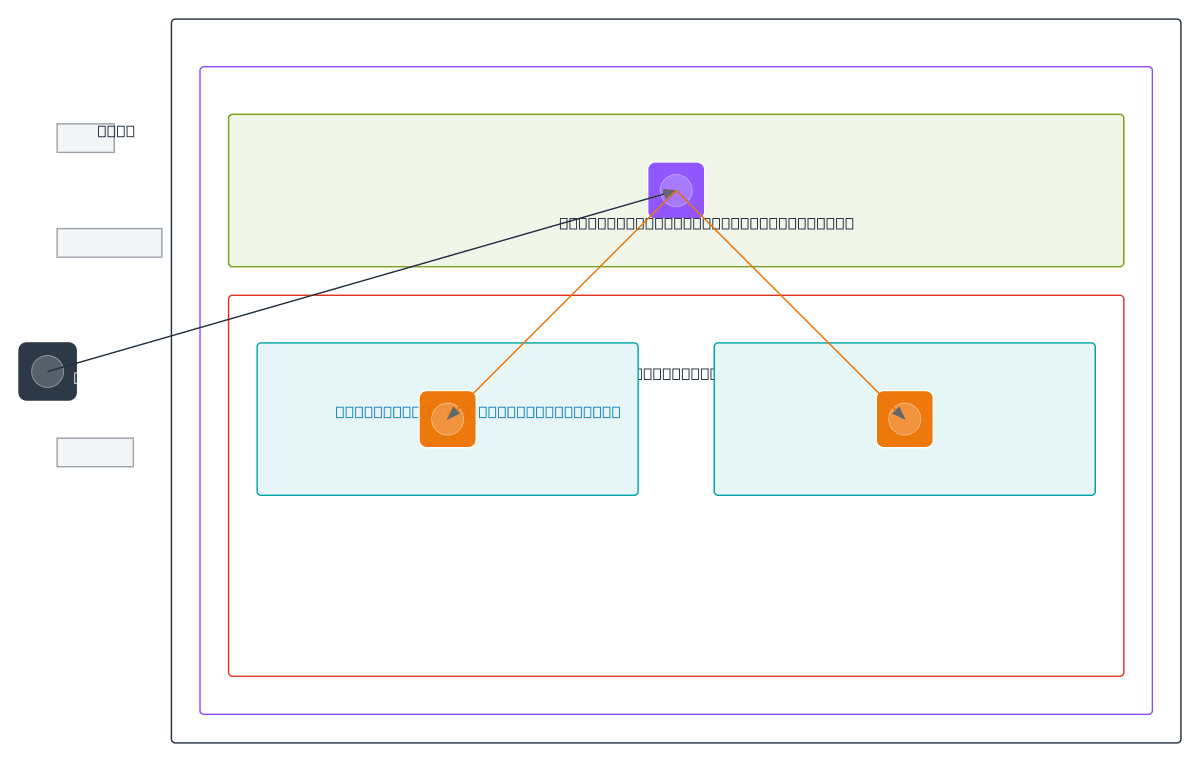
AWS VPC Internal ALB and Private Subnets
About This Architecture
Internal Application Load Balancer distributing traffic across EC2 instances in private subnets within a VPC. Users connect to the ALB in the public subnet, which routes requests to t3.medium EC2 instances deployed across Private Subnet A and Private Subnet B using the 10.0.0.0/16 CIDR block. This architecture isolates application servers from direct internet exposure while maintaining high availability through multi-AZ deployment and load balancing. Fork this diagram on Diagrams.so to customize security groups, add NAT gateways, or extend with RDS backends. Consider adding a Network ACL layer for defense-in-depth if your compliance requirements demand additional network segmentation.
People also ask
How do I set up an internal Application Load Balancer in AWS VPC to distribute traffic to EC2 instances in private subnets?
This diagram shows a VPC (10.0.0.0/16) with an ALB in a public subnet routing traffic to t3.medium EC2 instances in Private Subnet A (10.0.1.0/24) and Private Subnet B (10.0.2.0/24). The security group controls access between the ALB and application tier, ensuring instances remain isolated from direct internet exposure while maintaining high availability through multi-AZ load balancing.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing highly available internal applications
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.