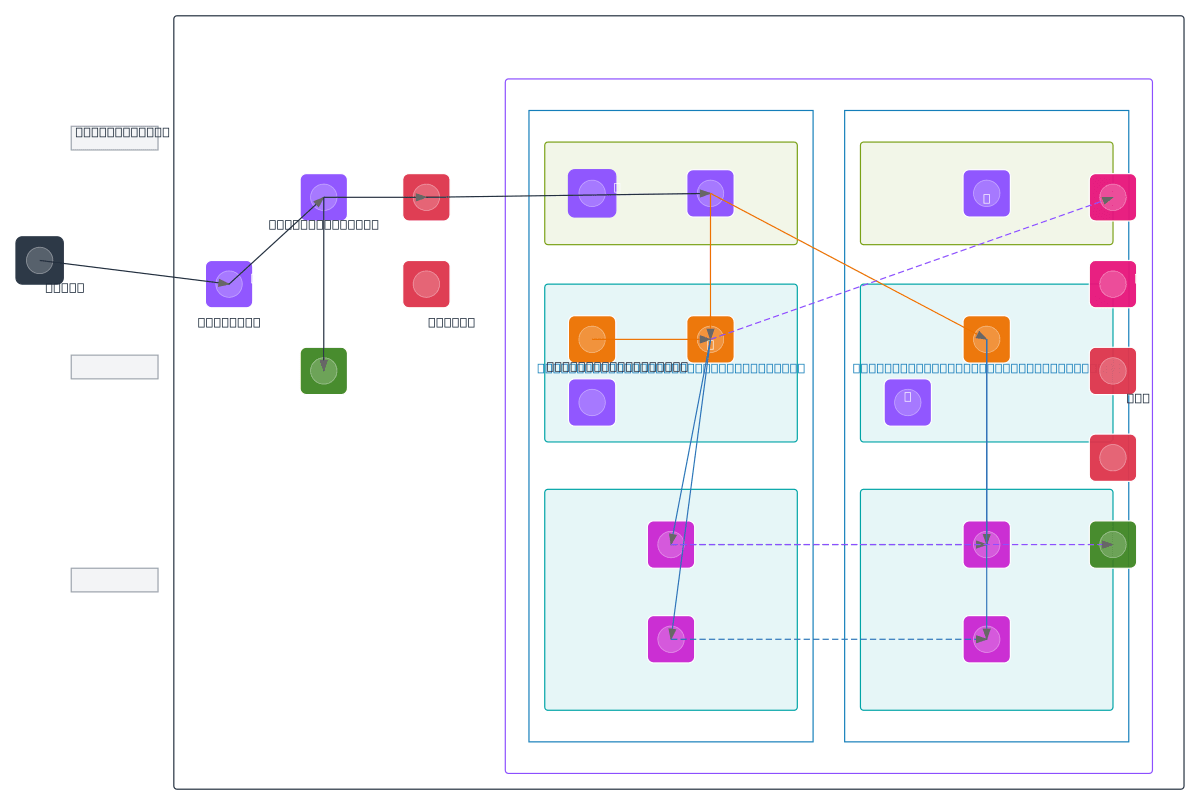
AWS Three-Tier Web App - Multi-AZ PostgreSQL
About This Architecture
Multi-AZ three-tier web app combining Route 53 DNS, CloudFront CDN, WAF, and Shield for global delivery and DDoS protection. Application tier spans two availability zones with Auto Scaling Groups of EC2 t3.medium instances behind Application Load Balancers, while data tier uses RDS PostgreSQL primary-replica pairs and ElastiCache clusters for read scaling and fault tolerance. Private subnets isolate app and database tiers, NAT Gateways enable outbound connectivity, and Secrets Manager secures credentials. CloudWatch monitors performance, CloudTrail audits API activity, and S3 stores automated backups for disaster recovery. Fork this diagram to customize instance types, subnet ranges, or add additional regions for your production workload.
People also ask
How do I design a highly available three-tier web application on AWS with multi-AZ failover and read scaling?
This diagram shows a production-grade AWS architecture using Route 53 for DNS, CloudFront CDN with WAF and Shield for edge delivery and DDoS protection, Auto Scaling EC2 instances across two availability zones behind Application Load Balancers, RDS PostgreSQL primary-replica pairs for database failover, and ElastiCache clusters for read-heavy workloads. Secrets Manager, CloudWatch, and CloudTrail
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing highly available web applications
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.