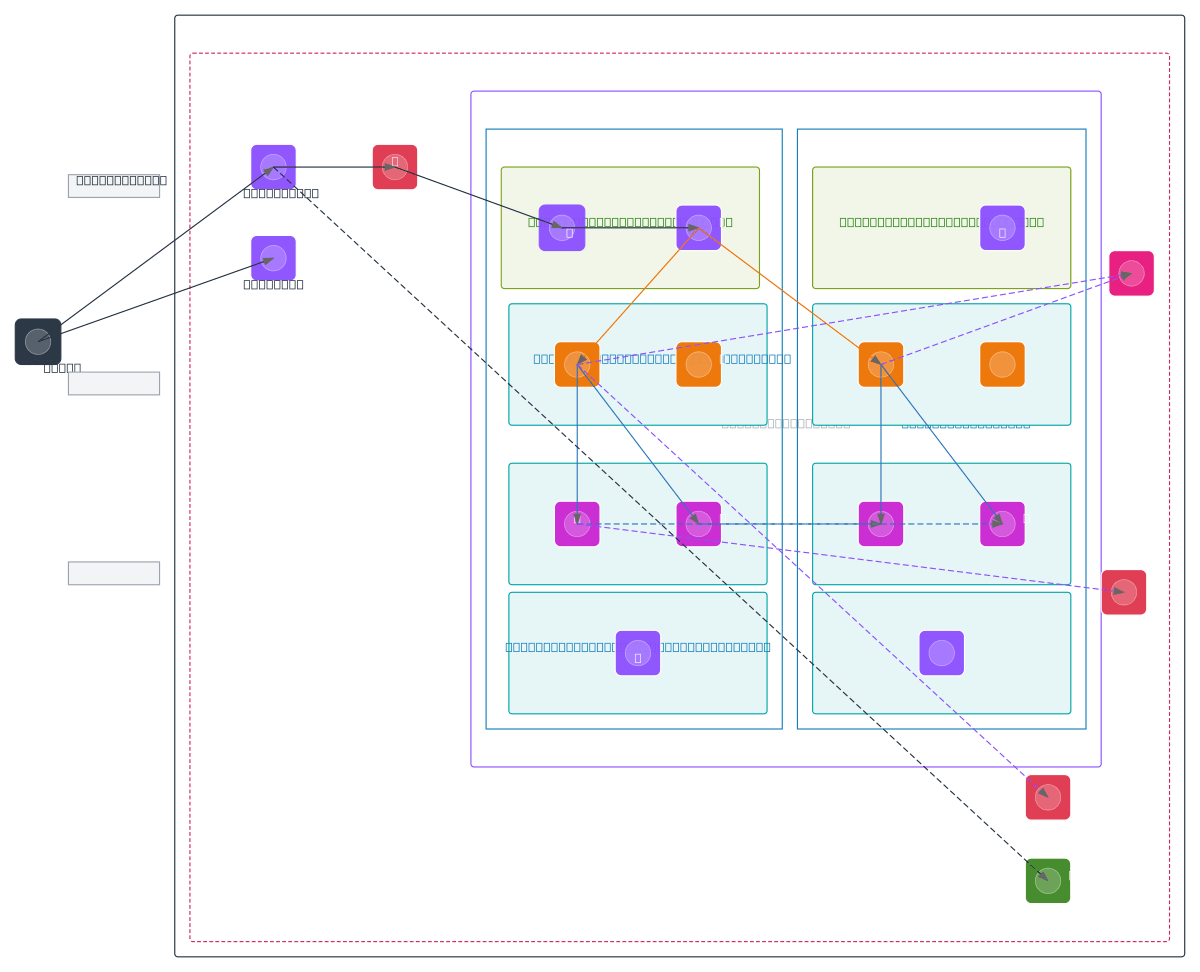
AWS Secure Three-Tier Multi-AZ Architecture
About This Architecture
AWS Secure Three-Tier Multi-AZ Architecture combines CloudFront, WAF, and Route 53 at the edge to protect and distribute user traffic across two availability zones. Application tier runs ECS Fargate containers behind Application Load Balancers, while data tier isolates RDS Aurora and ElastiCache with read replicas for resilience. Private subnets enforce least-privilege network segmentation, with Secrets Manager and KMS encryption protecting sensitive data and credentials. This pattern demonstrates production-grade security, high availability, and disaster recovery best practices for enterprise workloads. Fork and customize this diagram on Diagrams.so to match your VPC CIDR ranges, AZ selections, and scaling requirements.
People also ask
How do I design a highly available, secure three-tier AWS application across multiple availability zones?
This diagram shows a production AWS architecture spanning two AZs with CloudFront and WAF for edge protection, ECS Fargate for containerized apps, RDS Aurora with standby replicas for data resilience, and ElastiCache for caching. Private subnets isolate each tier, Secrets Manager protects credentials, and KMS encrypts sensitive data at rest.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing highly available, secure multi-AZ applications
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.