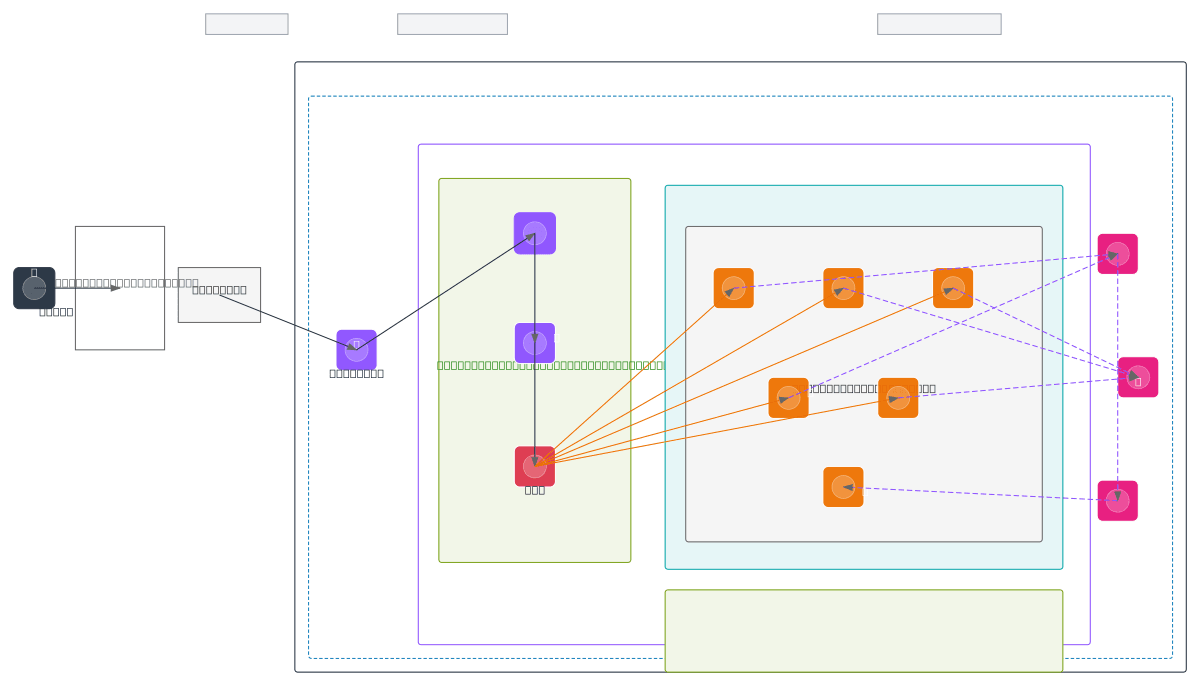
AWS Real-Time WebSocket Processing - Tokyo
About This Architecture
Real-time WebSocket processing architecture deployed in AWS Tokyo region (ap-northeast-1) using Route 53 DNS, ALB with WAF protection, and ECS Fargate tasks for stateful connection handling. Traffic flows from users through public internet to Route 53, then through Internet Gateway and ALB to five auto-scaled Fargate tasks behind WAF, ensuring DDoS protection and low-latency WebSocket connections. CloudWatch, CloudWatch Logs, and CloudWatch Alarms provide observability across the Core, Distribution, and Observability layers, enabling real-time monitoring and auto-scaling decisions. This architecture demonstrates best practices for highly available, secure WebSocket applications requiring sub-100ms latency in APAC regions. Fork this diagram on Diagrams.so to customize subnets, scaling policies, or add additional AWS services like ElastiCache or DynamoDB for session state.
People also ask
How do I architect a real-time WebSocket application on AWS in the Tokyo region with auto-scaling and DDoS protection?
This diagram shows a production-ready WebSocket architecture in ap-northeast-1 using Route 53 for DNS, ALB with WAF for DDoS protection, and five auto-scaled ECS Fargate tasks for stateful connection handling. CloudWatch Logs and Alarms provide observability and trigger scaling decisions, ensuring low-latency WebSocket connections for APAC users.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing real-time WebSocket applications in Asia-Pacific regions
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.