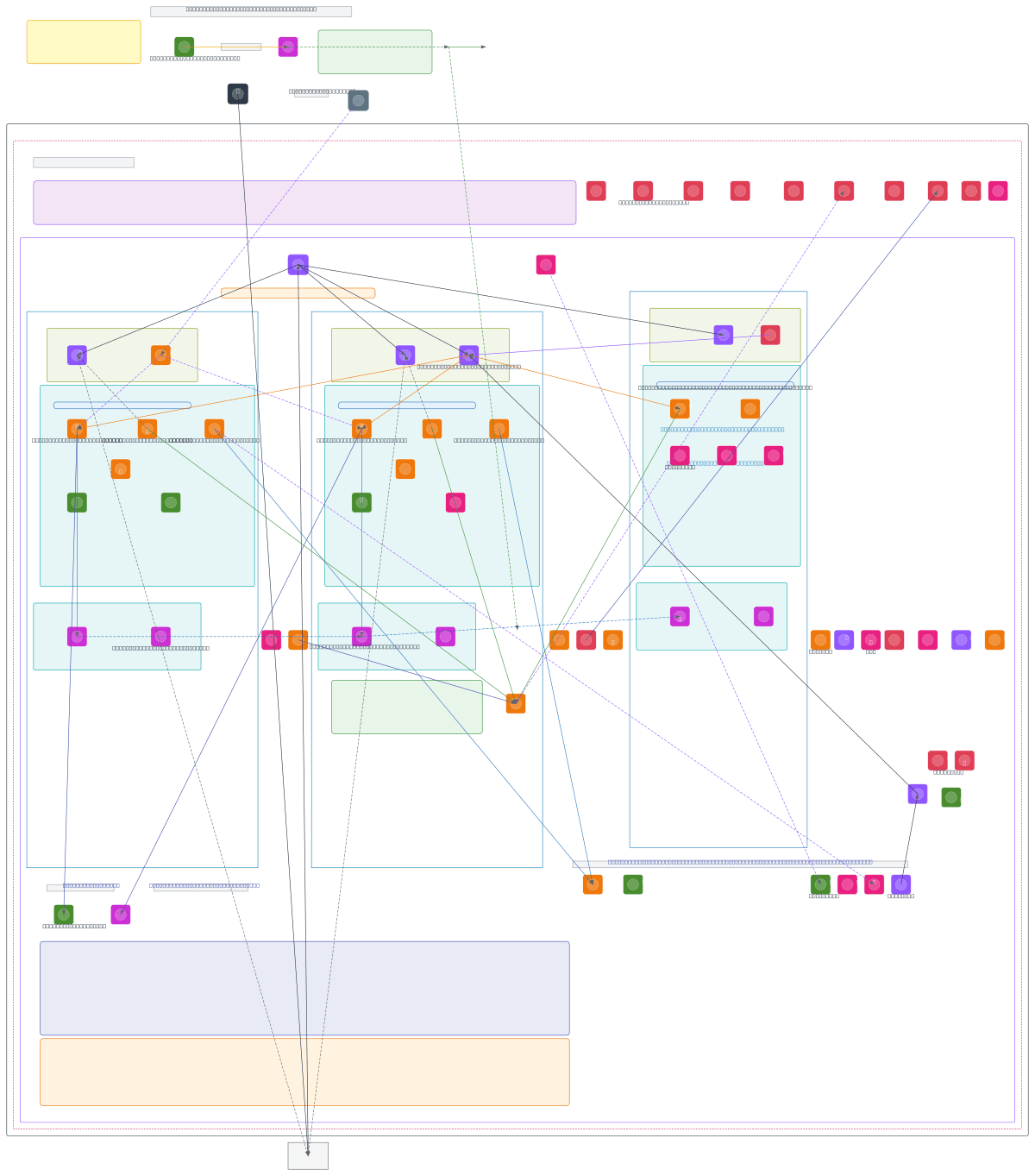
AWS Production EKS Multi-AZ Architecture
About This Architecture
Production-ready EKS multi-AZ architecture spanning us-east-1a, us-east-1b, and us-east-1c with Terraform-provisioned infrastructure, GitHub OIDC CI/CD integration, and comprehensive security controls. Infrastructure workflow begins with Bootstrap Bash Script and Terraform Execution, storing state in S3 with DynamoDB locking, then provisions IAM roles (cicd-role-prod, eks-cluster-role-prod, eks-node-role-prod), EKS Managed Control Plane, and worker nodes across three availability zones. Data layer includes RDS Aurora primary and replicas, ElastiCache clusters, DynamoDB tables, and SQS queues, all accessed via VPC Endpoints (S3, DynamoDB gateways and PrivateLink interfaces) to eliminate internet traversal. This architecture demonstrates zero-trust networking with private subnets, NAT Gateways per AZ, WAF protection, KMS encryption, CloudTrail auditing, and VPC Flow Logs—essential for regulated workloads requiring compliance and blast-radius isolation. Fork and customize this diagram on Diagrams.so to adapt subnet CIDRs, instance types, or add additional AWS services like SageMaker or Bedrock. Consider adjusting Auto Scaling Group thresholds and RDS instance classes based on workload profiling and cost optimization targets.
People also ask
How do I design a production EKS cluster across multiple AWS availability zones with Terraform, GitHub CI/CD, and zero-trust networking?
This diagram shows a three-AZ EKS architecture provisioned entirely via Terraform with GitHub OIDC authentication, eliminating long-lived credentials. Worker nodes auto-scale across us-east-1a/b/c, while RDS Aurora and ElastiCache replicate for high availability; all private subnets route to AWS services through VPC Endpoints (S3, DynamoDB gateways and PrivateLink interfaces) without internet expo
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing production-grade EKS clusters with multi-AZ resilience and infrastructure-as-code aut
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.