AWS Multi-AZ VPC with EKS and RDS
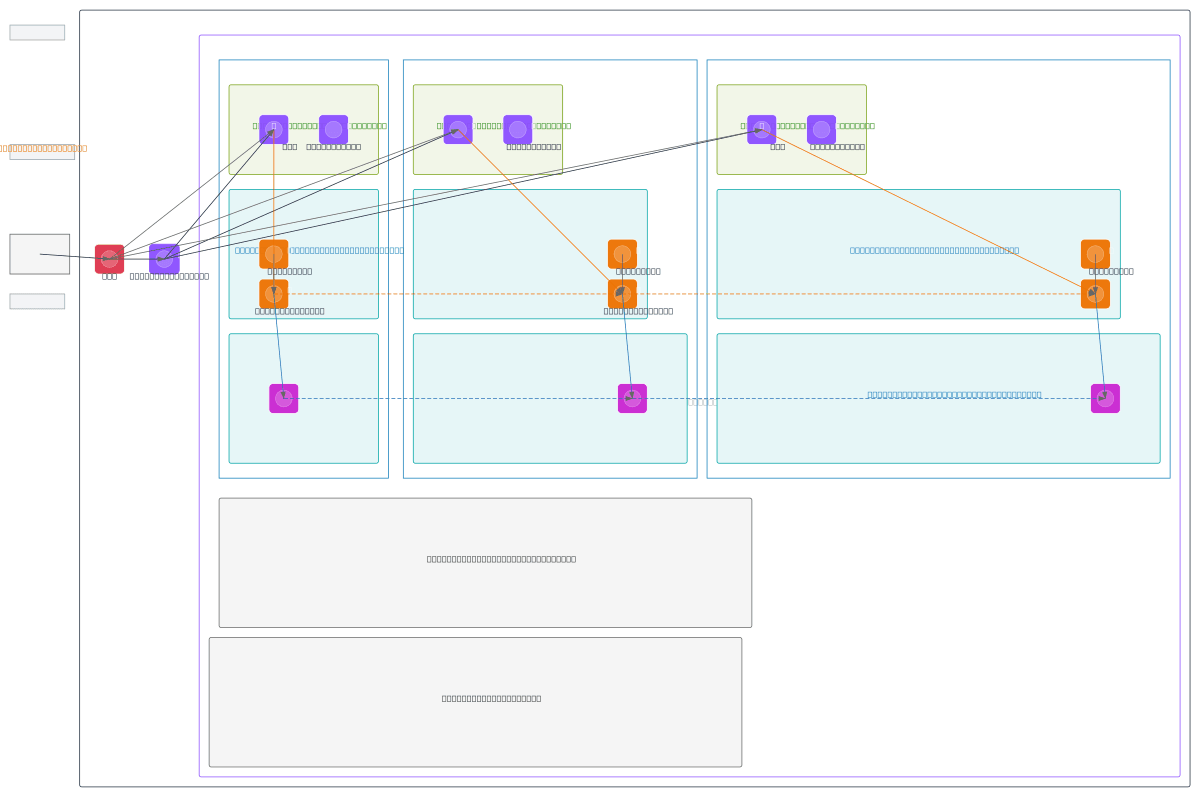
About This Architecture
Multi-AZ VPC spanning three availability zones with AWS WAF, Internet Gateway, and Application Load Balancers distributing traffic across EKS nodes. EKS cluster runs containerized workloads on nodes in private app subnets across AZ-1, AZ-2, and AZ-3, while RDS Multi-AZ cluster with primary, standby, and replica instances provides resilient database layer in isolated data subnets. NAT Gateways in each public subnet enable secure outbound connectivity from private subnets without exposing nodes to inbound internet traffic. This architecture demonstrates AWS best practices for fault tolerance, auto-scaling, and disaster recovery with zero single points of failure. Fork and customize this diagram on Diagrams.so to match your VPC CIDR ranges, instance types, or add additional AWS services like ElastiCache or Secrets Manager.
People also ask
How do I design a highly available AWS VPC with EKS and RDS across multiple availability zones?
This diagram shows a three-AZ AWS VPC (10.0.0.0/16) with WAF and Internet Gateway protecting traffic to Application Load Balancers, which route to EKS nodes in private app subnets. EKS cluster spans AZ-1, AZ-2, and AZ-3 with nodes communicating to RDS Multi-AZ instances (primary, standby, replica) in isolated data subnets, while NAT Gateways enable secure outbound connectivity.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing highly available Kubernetes infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.