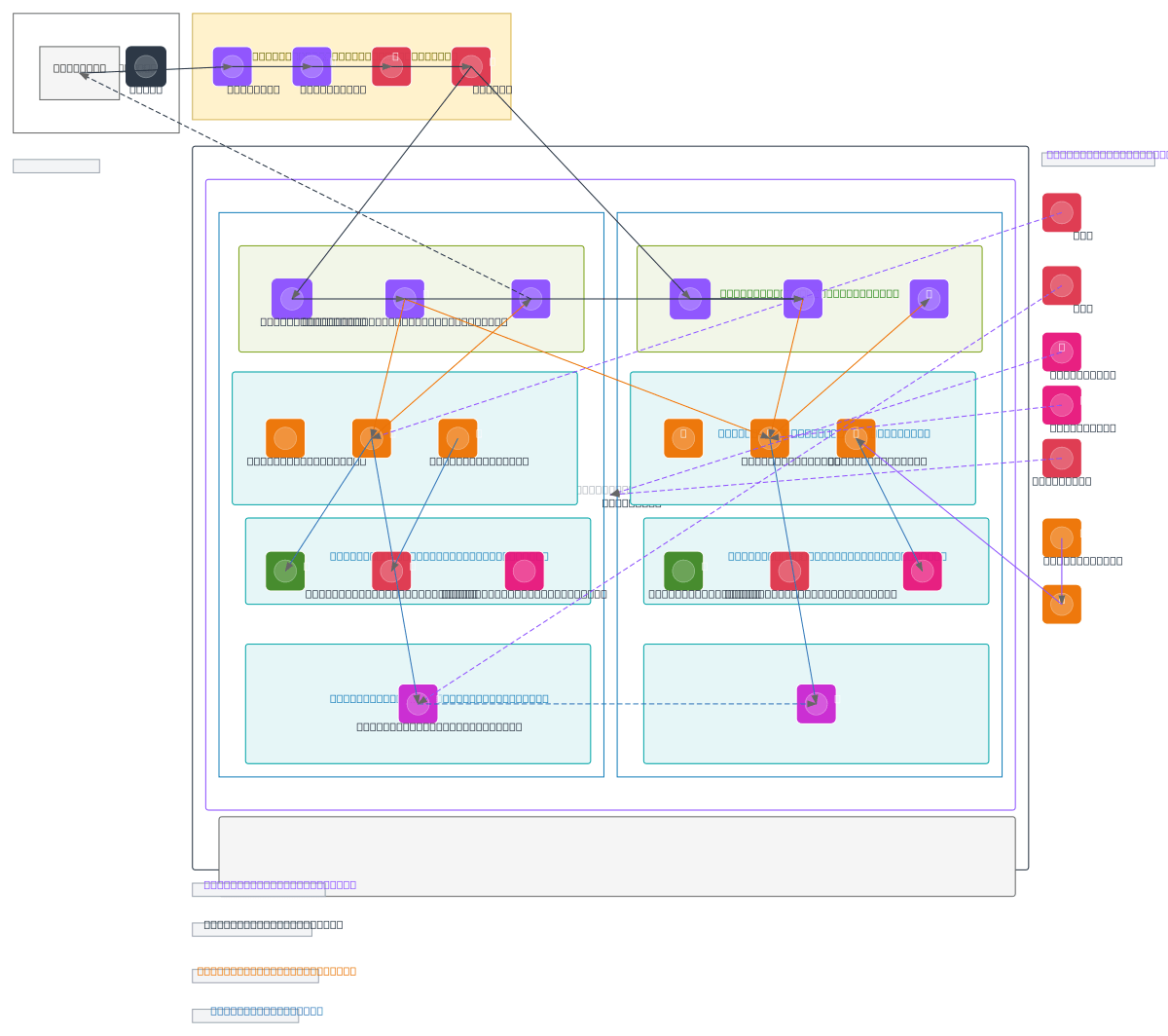
AWS Multi-AZ Network Architecture with CI/CD
About This Architecture
Multi-AZ network architecture spanning two AWS availability zones with Route 53 DNS, CloudFront CDN, WAF, and Shield DDoS protection fronting dual Application Load Balancers. Traffic routes through Internet Gateways to Auto Scaling Groups of t3.medium EC2 instances in private app subnets, with RDS Multi-AZ database failover between us-east-1a and us-east-1b. VPC Endpoints for S3, Secrets Manager, and CloudWatch enable secure private connectivity without NAT Gateway costs, while IAM, KMS encryption, CloudTrail auditing, GuardDuty threat detection, and CodePipeline CI/CD automation provide defense-in-depth security and compliance. Fork this diagram to customize subnets, instance types, or add additional AZs for your production environment. The architecture demonstrates AWS Well-Architected Framework principles: high availability through multi-AZ redundancy, security via least-privilege IAM and encryption, and operational excellence through automated CI/CD deployment.
People also ask
How do I design a highly available AWS multi-AZ network architecture with automatic failover and CI/CD deployment?
This diagram shows a production-ready AWS multi-AZ architecture spanning us-east-1a and us-east-1b with Route 53 DNS, CloudFront CDN, WAF, and Shield protecting dual Application Load Balancers that distribute traffic to Auto Scaling EC2 instances. RDS Multi-AZ database replication ensures data durability, VPC Endpoints provide secure private access to AWS services, and CodePipeline with CodeDeploy
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing highly available, secure multi-AZ production workloads
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.