AWS Fargate App - Tokyo Region (ap-northeast-1)
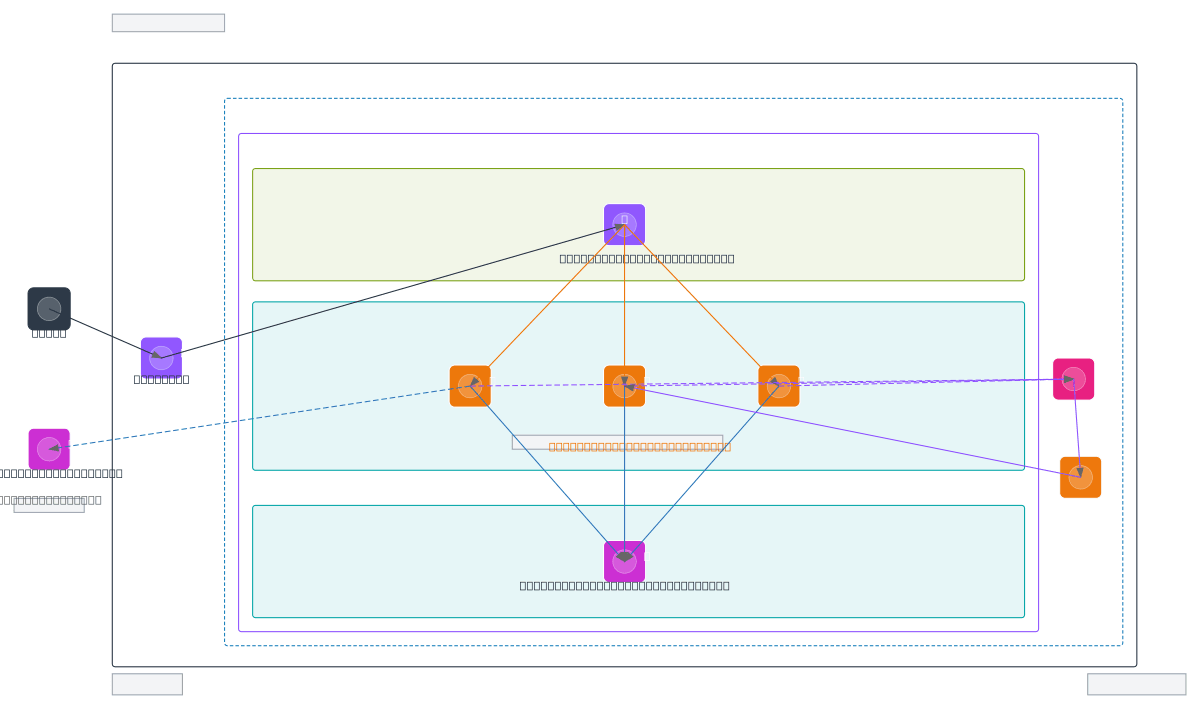
About This Architecture
Three-tier AWS Fargate architecture in ap-northeast-1 (Tokyo) uses Route 53 DNS routing to an Application Load Balancer distributing traffic across three auto-scaled Fargate tasks. The ECS cluster spans a public subnet for the ALB and a private application subnet hosting Fargate containers, with a separate private data subnet isolating a db.t3.medium RDS instance. CloudWatch monitors all Fargate tasks and triggers Auto Scaling policies to adjust container count based on demand, while external system integration and RDS connectivity demonstrate production-ready patterns. This architecture demonstrates high availability, cost efficiency, and operational observability for containerized workloads in AWS regions outside primary US zones. Fork and customize this diagram on Diagrams.so to adapt subnet CIDR blocks, instance types, or scaling thresholds for your Tokyo-region deployment.
People also ask
How do I design a scalable Fargate application architecture in AWS Tokyo region with load balancing and auto-scaling?
This diagram shows a production-ready three-tier Fargate architecture in ap-northeast-1 where Route 53 routes users to an Application Load Balancer, which distributes traffic across auto-scaled Fargate tasks in a private subnet. The tasks connect to a db.t3.medium RDS instance in an isolated data subnet, while CloudWatch monitors performance and triggers Auto Scaling policies to adjust container c
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing containerized applications in Tokyo region
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.