AWS Elastic Beanstalk Network Security Groups
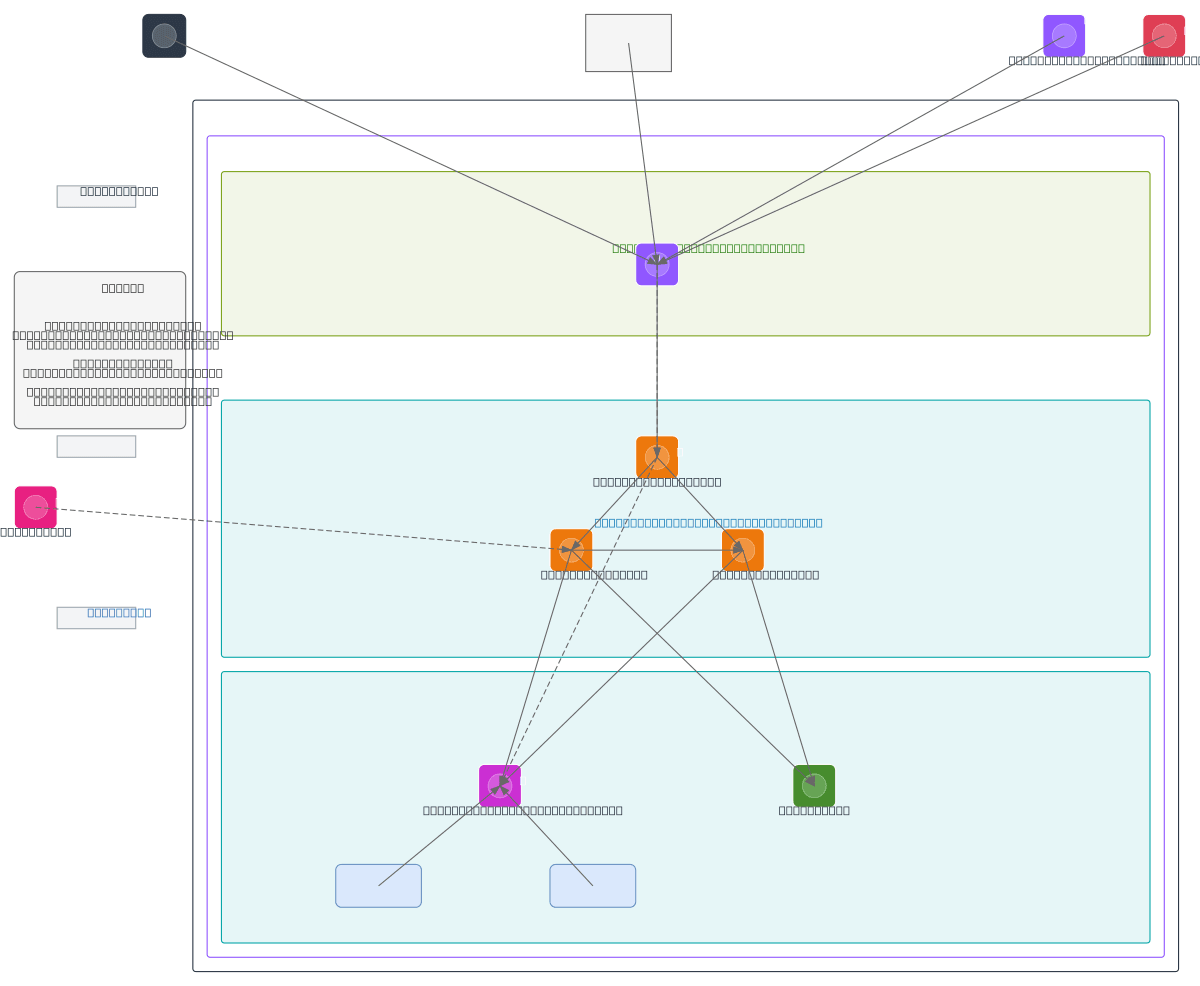
About This Architecture
Multi-tier AWS Elastic Beanstalk architecture with layered security groups enforcing least-privilege access across public, app, and data tiers. Internet and Office VPC traffic routes through an Elastic Load Balancer protected by RedShield WAF and Route 53 health checks, with separate security groups controlling ingress to EC2 Auto Scaling instances, RDS PostgreSQL, and Amazon EFS. Security group self-references and CIDR-based rules isolate the app tier from direct external access while enabling internal east-west communication. Fork this diagram to customize security group rules, add additional WAF rules, or adapt CIDR ranges for your VPC design. This architecture demonstrates AWS best practices for defense-in-depth networking in production Elastic Beanstalk environments.
People also ask
How do I design security groups for an AWS Elastic Beanstalk application with separate public, app, and data tiers?
This diagram shows a production-grade security group architecture where the Elastic Load Balancer accepts traffic from Internet and Office VPC through sg-lb1, RedShield WAF protects ingress on TCP 443, and the app tier EC2 instances in sg-asg1 and sg-asg2 communicate internally while accessing RDS PostgreSQL through sg-rds1 and Amazon EFS through sg-efs. Self-referencing security groups enable eas
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure Elastic Beanstalk deployments
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.