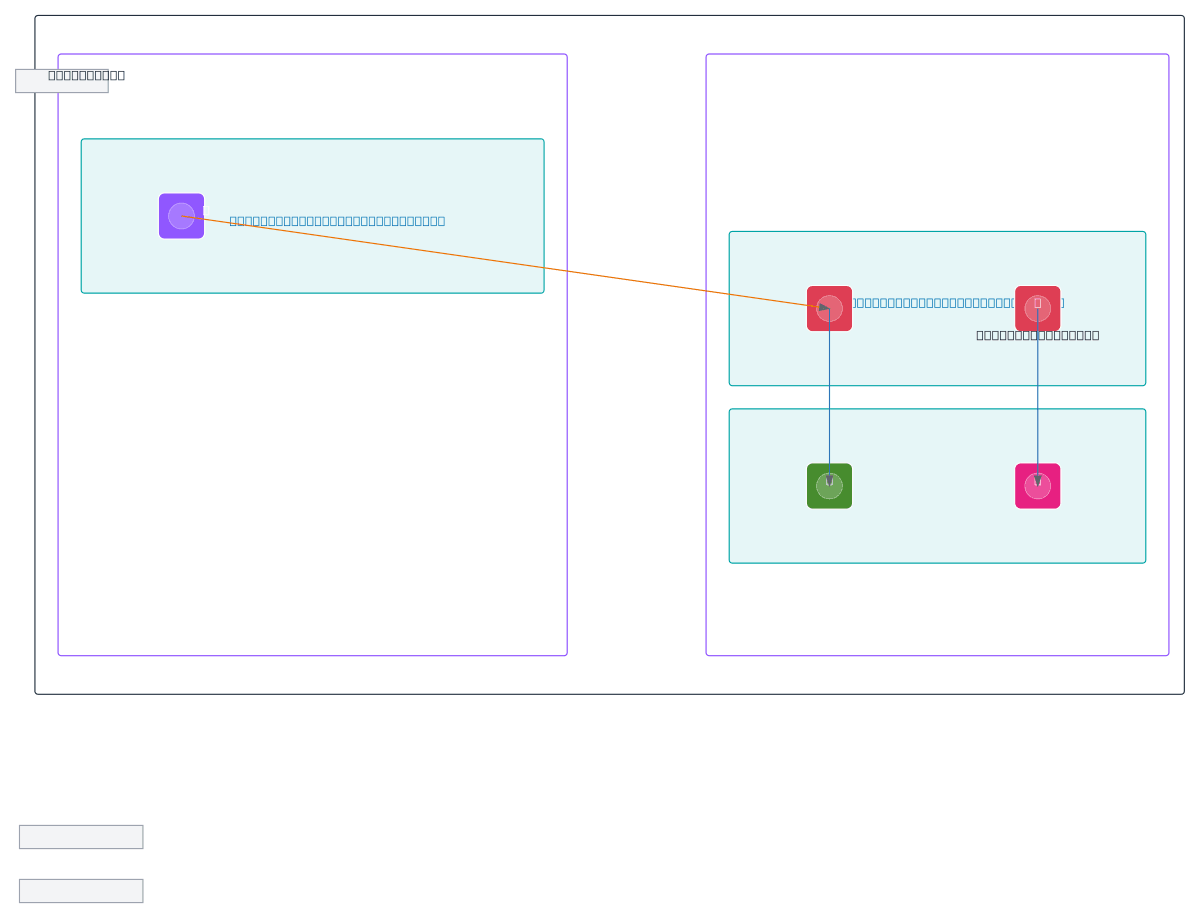
AWS Dual-VPC with PrivateLink to SageMaker
About This Architecture
Dual-VPC architecture with PrivateLink integration isolates SageMaker workloads in VPC B while enabling secure cross-VPC communication through VPC peering and interface endpoints. VPC A serves as the endpoint VPC, hosting a VPC endpoint that routes traffic to SageMaker Endpoint and model artifacts in S3, with VPC Flow Logs captured to a dedicated S3 bucket for audit and compliance. SageMaker Studio and the SageMaker Endpoint in VPC B's private subnets access CloudWatch Logs and model artifacts without traversing the public internet, reducing blast radius and enforcing least-privilege network access. Fork this diagram on Diagrams.so to customize subnet CIDRs, add additional endpoints, or integrate with your existing VPC topology and security policies. This pattern is ideal for regulated industries requiring network isolation, data residency compliance, and detailed traffic observability across ML infrastructure.
People also ask
How do I securely connect SageMaker workloads across multiple VPCs using PrivateLink without exposing traffic to the public internet?
This diagram shows a dual-VPC design where VPC A hosts interface endpoints that route traffic to SageMaker Endpoint and S3 buckets in VPC B via PrivateLink, eliminating internet exposure. VPC peering connects the VPCs, while VPC Flow Logs provide audit trails to S3, ensuring compliance and observability for regulated ML workloads.
- Domain:
- Cloud Aws
- Audience:
- AWS solutions architects designing secure multi-VPC ML infrastructure
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.