AWS Automated Incident Response Workflow
About This Architecture
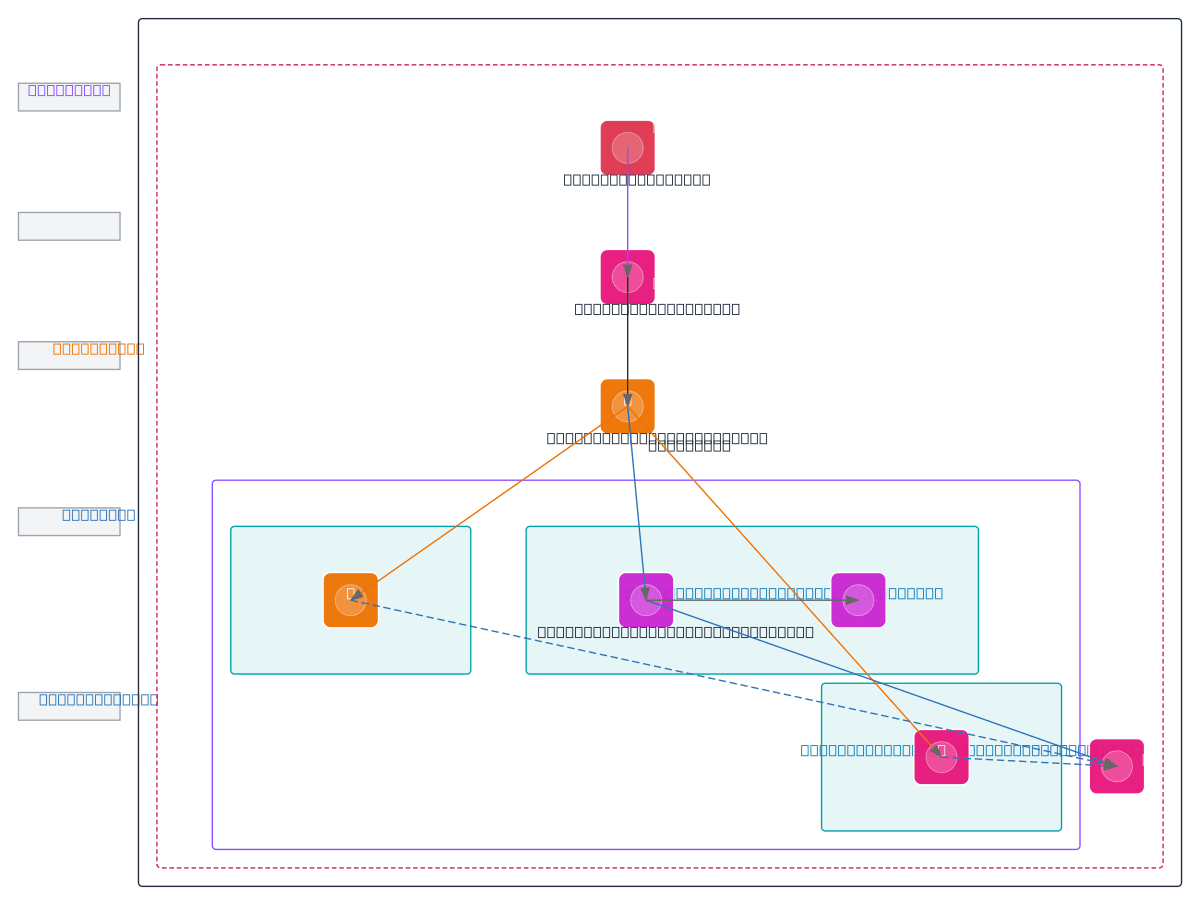
AWS Automated Incident Response Workflow orchestrates real-time threat detection and remediation using GuardDuty findings routed through EventBridge to Lambda functions. Detection triggers automatic quarantine of compromised EC2 instances via security group modifications, concurrent logging to DynamoDB, and email alerts via SNS. Observability is unified through CloudWatch Dashboard, which aggregates incident logs, quarantine status, and alert metrics for centralized monitoring. This architecture demonstrates infrastructure-as-code security automation that reduces mean time to response (MTTR) by eliminating manual incident triage. Fork and customize this diagram on Diagrams.so to adapt the workflow for your threat model, add additional response actions, or integrate with your SOAR platform.
People also ask
How can I automate incident response on AWS when GuardDuty detects a threat?
This diagram shows a complete automated workflow: GuardDuty findings trigger EventBridge rules that invoke Lambda functions to quarantine affected EC2 instances via security groups, log incidents to DynamoDB, send email alerts via SNS, and stream all events to CloudWatch Dashboard for real-time visibility. This reduces manual response time and ensures consistent remediation.
- Domain:
- Security
- Audience:
- Security architects and incident response engineers implementing automated threat detection and remediation on AWS
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.