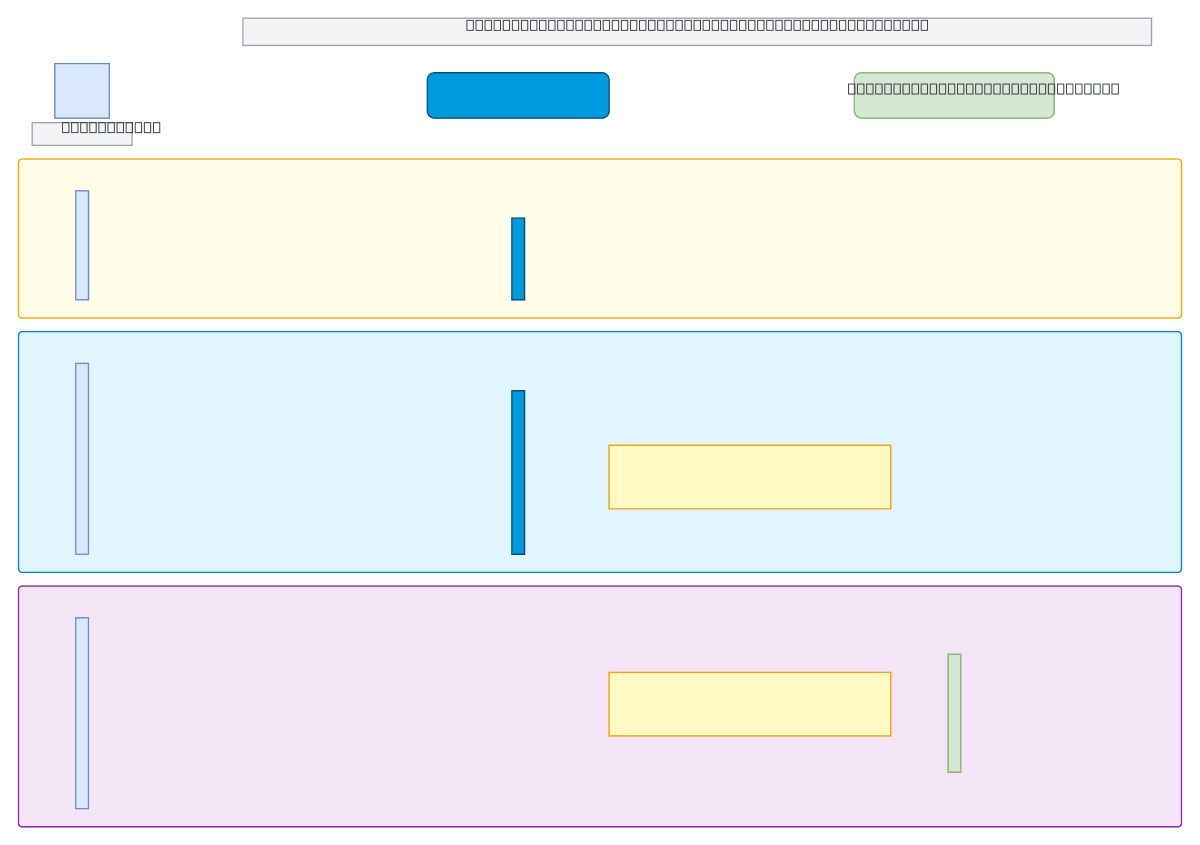
Akamai Admin - CSR Generation and CA Submission
About This Architecture
Akamai CSR generation and CA submission workflow orchestrates three phases: user authentication, certificate signing request creation, and CA signature submission. The sequence diagram shows interactions between the Akamai Admin console, authenticated users, and external certificate authorities, with the private key remaining securely stored within Akamai infrastructure. This architecture demonstrates secure certificate lifecycle management by separating key generation from CSR transmission and enforcing authentication gates at each phase. Fork this diagram on Diagrams.so to customize certificate workflows, document your PKI processes, or train teams on Akamai certificate provisioning. The design emphasizes that private keys never leave Akamai while CSRs containing public keys and domain information flow safely to CAs for signing.
People also ask
How does Akamai handle certificate signing request generation and submission to certificate authorities while protecting private keys?
Akamai's three-phase workflow authenticates users, generates CSRs containing public keys and domain information within the Admin console, then submits CSRs to CAs for signing—all while keeping private keys securely stored in Akamai infrastructure and never transmitted externally.
- Domain:
- Security
- Audience:
- Security architects and certificate administrators managing SSL/TLS certificates on Akamai CDN
Generated by Diagrams.so — AI architecture diagram generator with native Draw.io output. Fork this diagram, remix it, or download as .drawio, PNG, or SVG.